OT & ICS Cyber Defense
Engineered for Industrial Reality
Mach Defense designs and hardens industrial control system and operational technology environments where safety, uptime, and physical impact take priority over theoretical risk.
- ■ OT & ICS security architecture design
- ■ Secure PLC, SCADA & HMI configurations
- ■ Network segmentation & Purdue-aligned zoning
- ■ Industrial protocol risk reduction
- ■ Practical, operator-ready mitigation guidance

OT & ICS Cybersecurity Is Not IT Security
Industrial environments operate under constraints that traditional IT security models fail to account for, including safety risks, physical processes, legacy systems, and real‑world operational impact.
Cyber‑Physical Consequences
In OT environments, cybersecurity failures can directly affect physical processes from production outages to equipment damage and safety incidents. Security decisions must account for how systems behave in the real world, not just how data is protected.
Engineering‑Driven Security
Effective OT security is built into system architecture, network design, and operational procedures. Controls must be predictable, maintainable, and aligned with how engineers and operators actually work.
Availability Comes First
Unlike IT environments, downtime is often the greatest risk. Security measures must enhance resilience and segmentation without introducing instability or operational friction.
What Defensive OT/ICS Security Focuses On
- ■ Secure OT network architecture and zoning strategies
- ■ Resilient PLC, SCADA, and HMI configurations
- ■ Controlled trust boundaries between IT and OT environments
- ■ Risk reduction without disrupting safety or operations
- ■ Controls that operators and engineers can actually sustain
Typical OT/ICS Environment
Industrial networks commonly include a mix of legacy controllers, modern systems, vendor equipment, and operational workstations. Security engineering focuses on understanding these relationships and deliberately shaping trust, communication, and failure modes.
Defensive OT Security Requires Engineering Judgment
Industrial cybersecurity is shaped by physical processes, operational constraints, and long system lifecycles. Effective defense comes from engineering decisions made with these realities in mind.
Architecture First
Security in OT environments is established through network design, zoning, and trust boundaries, not by deploying tools on top of fragile systems.
Built for Operations
Defensive controls must be predictable, support maintenance workflows, and respect safety and uptime requirements across plants and facilities.
Designed to Last
OT systems often remain in service for decades. Security engineering must account for long‑term maintainability, vendor dependencies, and change control.

Mach Defense works with organizations when architectural decisions, operational constraints, or systemic risk warrant focused, engineering‑level cybersecurity guidance.
Engineering Defensive Readiness Across OT Environments
Effective OT cybersecurity depends on visibility, control, and resilience engineered across the full operational lifecycle, not point solutions applied after the fact.
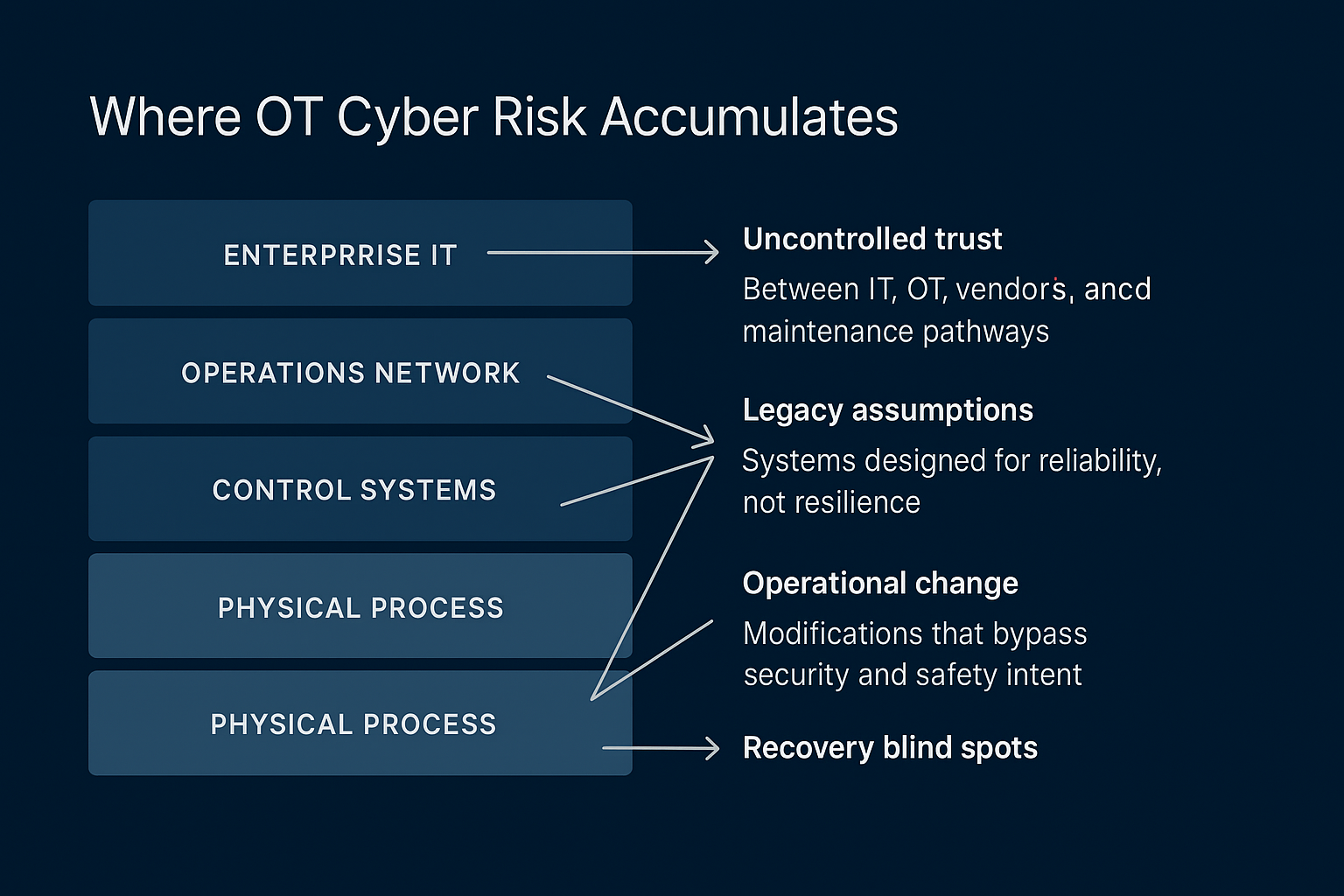
Where OT Cyber Risk Accumulates
- Uncontrolled trust
Between IT, OT, vendors, and maintenance pathways - Legacy assumptions
Systems designed for reliability, not resilience - Operational change
Modifications that bypass security and safety intent - Recovery blind spots
When failure modes are poorly understood or untested
When OT Cyber Risk Is Unmanaged vs. When It Is Managed
Unmanaged OT/ICS Risk
- • Loss of visibility during abnormal conditions
- • Safety systems treated as implicit protection
- • Changes made outside of security intent
- • Recovery dependent on tribal knowledge
- • Risk addressed only after incidents
Managed OT/ICS Security
- • Clear control boundaries and failure modes
- • Security aligned with safety and operations
- • Controlled, auditable change paths
- • Predictable recovery under degraded conditions
- • Risk reduced before incidents occur